Executive Summary
Organizations replacing an existing login provider typically need more than a simple refresh of the login screen. What they require is a secure and adaptable identity control plane, one that can seamlessly support B2C customers, B2B partners, and internal workforce users while integrating cleanly into the existing enterprise application and infrastructure landscape.
This blog examines such a scenario: an organization planning to replace its Microsoft ADFS–based login provider while operating across both SAP and Microsoft technology estates. The identity platforms evaluated as part of this assessment were SAP Customer Data Cloud (CDC), SAP Cloud Identity (Identity Authentication Service / IAS), AuthO, and Microsoft Entra External Identities (EEID).
- SAP CDC stands out for customer identity, privacy, and consent-led B2C use cases.
- AuthO brings strong developer ergonomics and flexible customer experience flows but adds another strategic supplier and often needs companion services for broader consent analytics or enterprise reporting.
- SAP CI (IAS) is best understood as a strong SAP-oriented workforce and federation layer, especially where SAP BTP and Fiori are central to the estate.
- Microsoft EEID ultimately aligned best because it met the mandatory criteria while aligning best with the client’s broader infrastructure services and modernization path away from ADFS.
Why the Identity Provider Choice Matters
A modern login provider is no longer just an authentication service. It becomes the decision point for single sign-on, single logout, federation, adaptive security, self-service journeys, machine identities, and session policy. In a hybrid SAP-and-Microsoft landscape, the provider also influences how much customization is needed in downstream applications and how quickly future channels can be onboarded.
That is why this comparison goes beyond feature checklists. It considers business fit across customer, partner, and workforce journeys; non-functional considerations such as deployment options and operational visibility; and strategic alignment with the surrounding platform ecosystem.
Target-State Architecture
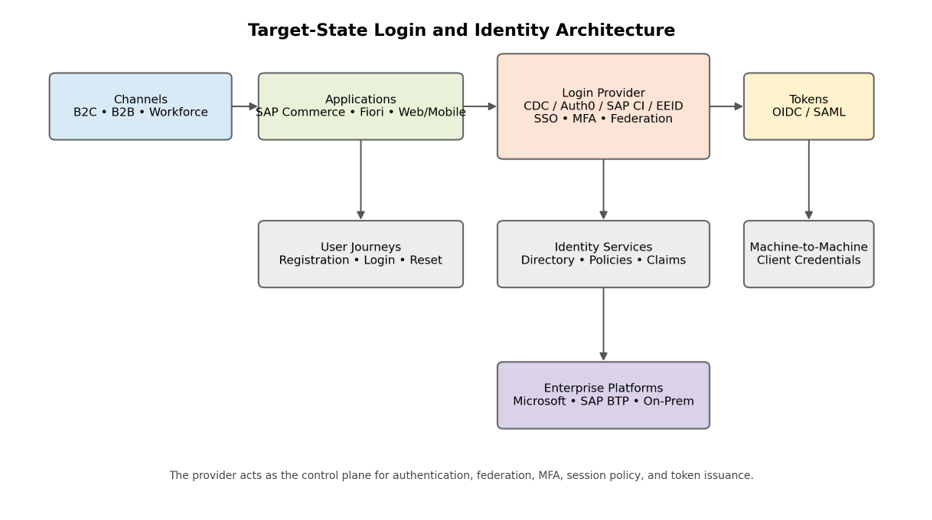 Architecture Callouts
Architecture Callouts
- The login provider becomes the control plane for authentication, federation, MFA, token issuance, and session policy.
- B2C and B2B experiences can share a common provider, but the provider must support very different operating models: customer-centric journeys, partner federation, and workforce-grade assurance.
- Machine-to-machine support matters when APIs and back-end integrations need standards-based client credentials.
- Deep alignment to SAP or Microsoft reduces customization effort in connected applications, especially for Fiori, directory synchronization, and enterprise security operations.
Evaluation Scope and Framing
The original assessment set out to identify a replacement for Microsoft ADFS and explicitly included the following scope dimensions:
- Support for external customers (B2C), business users and partners (B2B), and internal workforce users.
- Single Sign-On (SSO) and Single Logout (SLO).
- Federation with organizations, identity providers, cloud applications, and on-premises environments.
- Multi-factor authentication (MFA).
- Machine-to-machine authentication patterns.
- Integration compatibility with SAP and Microsoft platforms already in the client landscape.
This broad scope matters because some providers are designed first for customer identity, some for workforce or SAP-centric federation, and some for enterprise external identities anchored in Microsoft infrastructure. The best overall choice therefore depends on how these needs are prioritized together, not in isolation.
Shortlisted Providers briefly
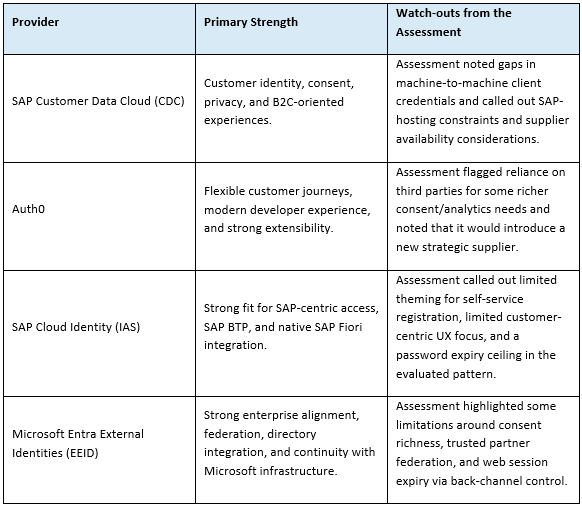
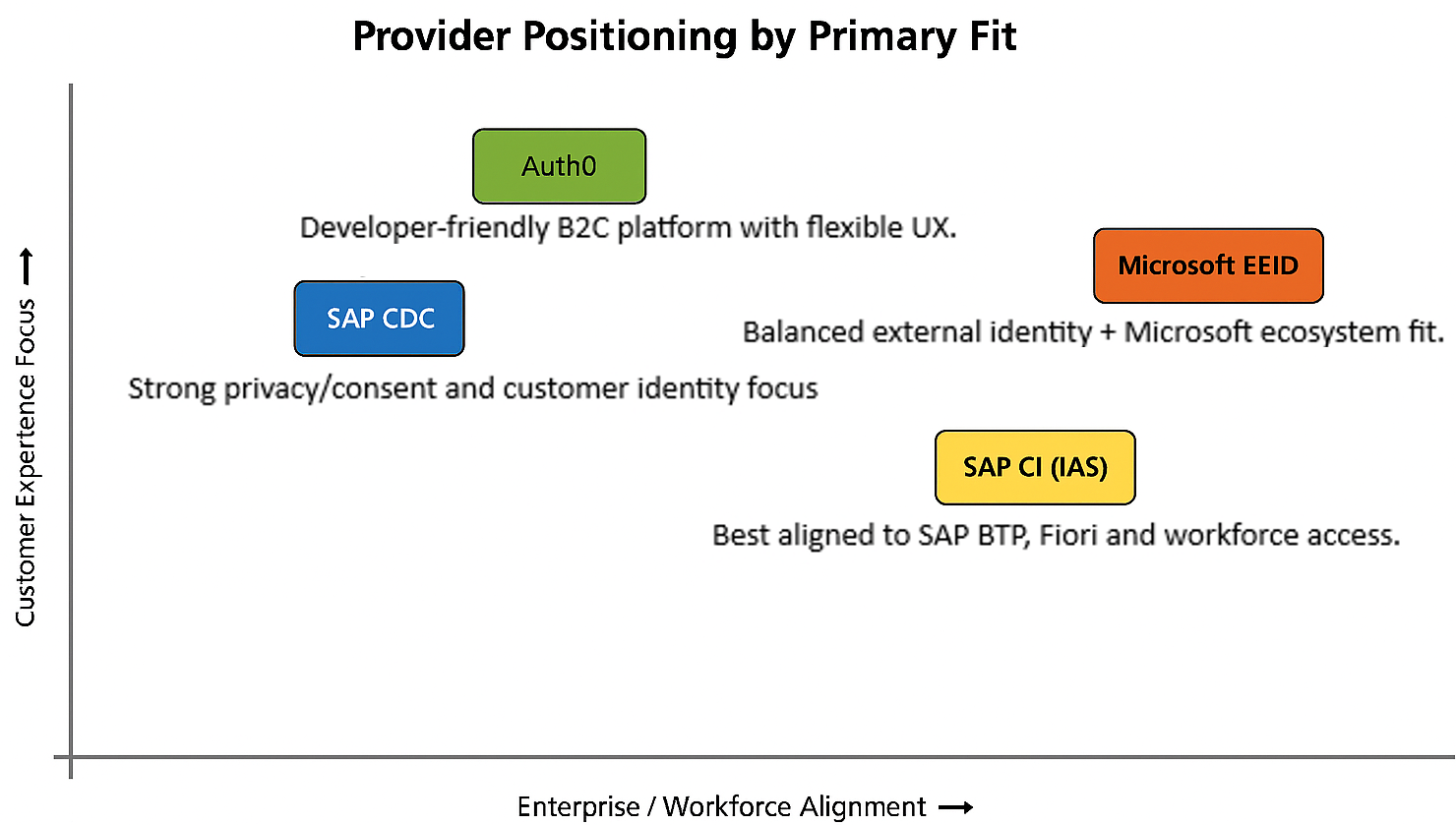
How the Providers Cluster by Primary Fit
What the Assessment Really Says
The source assessment does not treat all platforms as interchangeable. Instead, it reveals that each option is strongest in a different operating model. SAP CDC is B2C-led and shines where privacy and customer identity management are central. AuthO is also B2C-friendly, but its strength is flexibility and developer control. SAP CI (IAS) is most compelling in SAP-oriented workforce and federation scenarios. Microsoft EEID scores as the most natural continuation in a Microsoft-heavy identity architecture, especially when the goal is to modernize ADFS rather than introduce a radically different control plane.
Just as importantly, several limitations in the assessment are subtle but strategic. A provider might support sign-in and federation, yet still create friction because of weak analytics, constrained theming, deployment restrictions, or lack of back-end client credentials. These operational factors often matter more over a three-year horizon than a narrow comparison of login screens.
Qualitative Evaluation Summary
The table below distills the differentiators and explicit constraints that were called out in the assessment. It is intentionally selective: where the source matrix did not highlight a concern, the table uses “Not flagged” rather than assuming superiority.
Evaluation Area
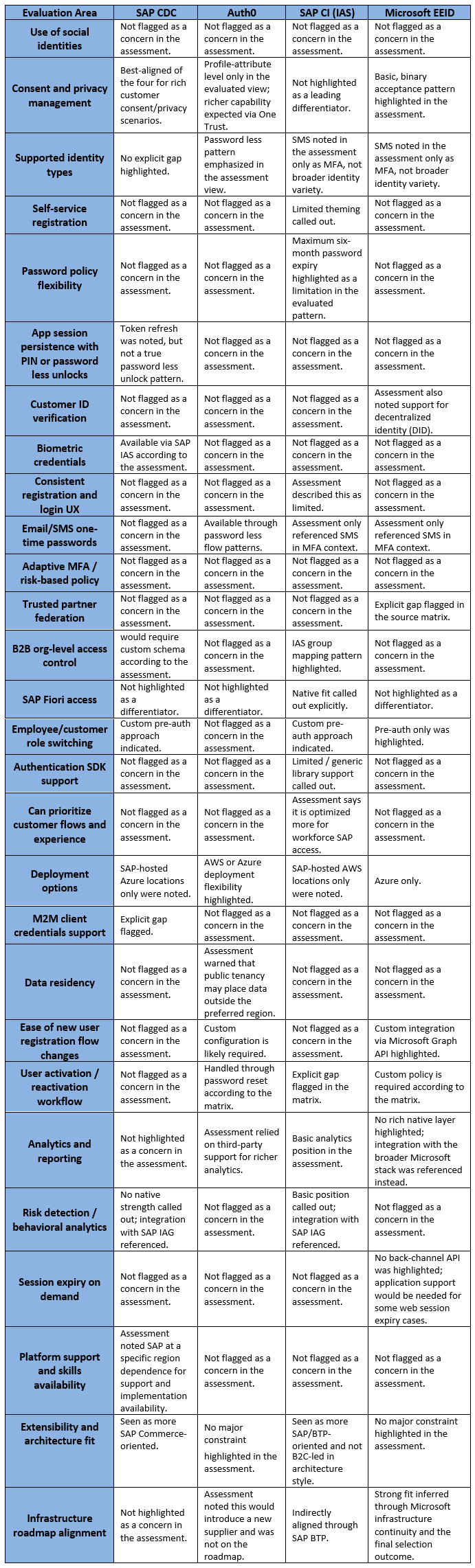
How to Read the Above Table
- The source matrix was qualitative rather than numeric, so this blog deliberately avoids inventing scores that were not present in the original assessment.
- “Not flagged” means the matrix did not call out a specific concern in that area; it should not be interpreted as a universal best-in-class rating.
- The most important signals come from the explicit limitations and differentiators because those are what shaped the final decision.
Why Microsoft EEID Was Selected
The final recommendation favored Microsoft Entra External Identities (EEID) because it was the best overall fit, not because it dominated every single category. A platform can be strongest for customer consent or front-end flexibility and still lose if it creates more friction in federation, infrastructure alignment, operational tooling, or future modernization paths.
EEID aligned with the client’s broader infrastructure services and met the mandatory functional criteria. In practical terms, this means less architectural disruption when replacing ADFS, better continuity with Microsoft-centric security and identity operations, and a more direct path to supporting external identities without introducing a new strategic platform where it is not needed.
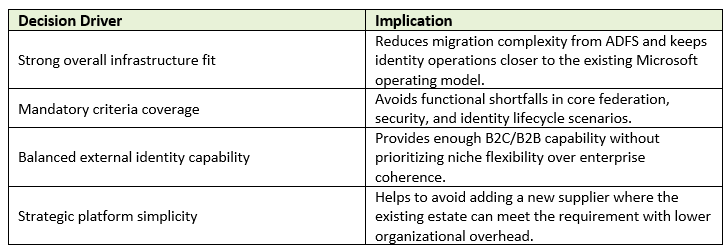
Trade-Offs to Keep in Mind
- If the primary mission were rich customer consent orchestration and consumer identity depth above all else, SAP CDC would deserve stronger consideration.
- If the priority were highly customized customer journeys and developer-led extensibility across many digital channels, AuthO could be attractive despite supplier and integration trade-offs.
- If the requirement centered on SAP-first workforce federation and Fiori access, SAP CI (IAS) would be a very natural fit.
- Because this evaluation balanced B2C, B2B, workforce, SAP integration, and Microsoft infrastructure together, EEID became the best-fit choice rather than the best niche performer.
Migration Considerations for an ADFS Replacement Program
- Inventory existing relying parties, protocols, and claims mappings before selecting the target provider configuration.
- Separate customer, partner, and workforce journeys so the operating model is clear before migration begins.
- Prioritize high-value federation and SSO use cases first, then move self-service registration, password reset, and step-up authentication scenarios.
- Validate machine-to-machine and API client credential needs early, because this is often overlooked in login modernization projects.
- Define a session-management strategy at application level where the provider has limited back-channel session invalidation support.
Conclusion
Choosing a login provider is a platform decision, not just a feature selection exercise. The strongest solution is the one that supports the customer user journeys, security posture, operating model, and platform roadmap together. In this assessment, Microsoft Entra External Identities (EEID) delivered the best aggregate fit for replacing ADFS in a mixed SAP and Microsoft environment. CDC, AuthO, and SAP CI each remain strong options in more specialized patterns, but EEID provided the clearest path to a secure, scalable, and strategically aligned identity foundation.