Over the last few years, the workplace has changed a lot. The traditional office setups with company-assigned desktops and desk phones are the things of the past. Now, employees work from anywhere using personal and corporate devices across multiple networks.
Unified Communications (UC) platforms enable seamless collaboration through voice, video, messaging, screen and file sharing. However, this connectivity brings security risks—AI-driven phishing, deepfakes, and ransomware attacks threaten sensitive data.
Organizations must ensure only authorized users access their systems and comply with regulations like GDPR, HIPAA, FedRAMP, DoDIN APL in order to protect the organization from the security attacks.
This blog explores the latest UC security standards, privacy and compliance frameworks, that organizations must adopt to safeguard user and enterprise data in an era of hybrid and AI-driven communications.
1. FIPS (Federal Information Processing Standards)
FIPS is a United States standard for approving cryptographic modules. Unified Communications (UC) vendors need FIPS certification to sell products to government agencies and industries like defense, finance, and healthcare. It is a NIST standard and required for both Common Criteria certification and DoDIN APL listing.
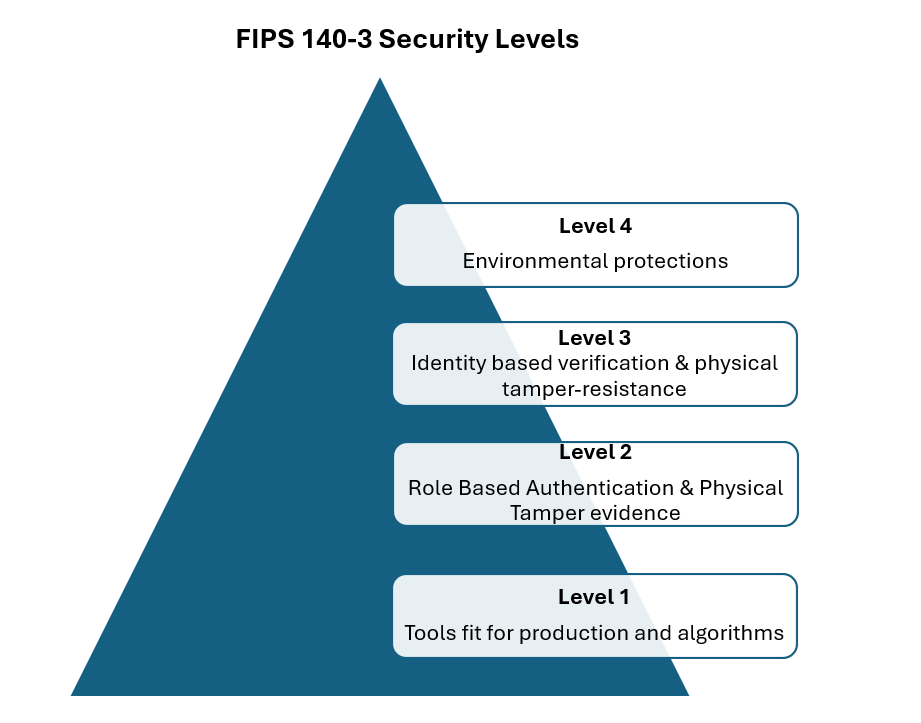
FIPS 140-3 became effective since 2019, FIPS certification lasts five years. It has four security levels with Level 4 as the highest and Level 1 as the lowest. Cryptographic Module Validation Program (CMVP), executed by the U.S. and Canada, certifies UC products for secure use in sensitive industries.
All CMVP tests are run by independent labs recognized by NVLAP (National Voluntary Laboratory Accreditation Program) to evaluate cryptographic modules. CMVP certified products can be found here CMVP
FIPS 140-3 aligns with the international standards for security and testing needs, ensuring global consistency and interoperability.
2. Common Criteria (CC)
CCs a global standard used to evaluate the security of products. It was developed by the governments of Canada, France, Germany, the Netherlands, the UK, and the US and is and is recognized by over 30 countries worldwide.
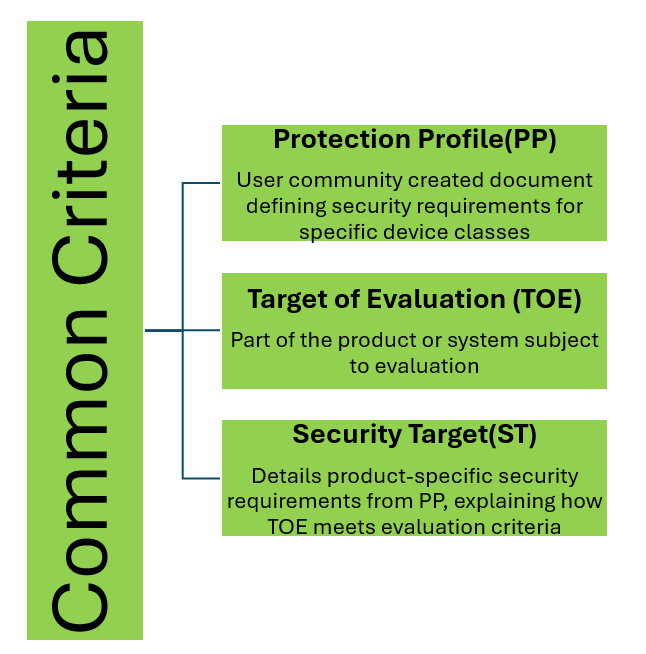
CC establishes a hierarchical framework of security concepts and terminology. Its structure is as follows:
The Common Criteria Certification Process
To certify a product under Common Criteria (CC), vendors follow these steps.
- Security Target (ST) preparation: The vendor drafts an ST, outlining security functions, capabilities, intended use, protection profile, and target evaluation assurance level.
- Laboratory Evaluation: An independent testing laboratory, accredited by the Common Criteria Recognition Arrangement (CCRA), reviews the product against CC standards, verifying security claims and testing for vulnerabilities.
- Certification Issuance – Upon successful evaluation, the product receives CC certification, assuring customers of independently verified security
While the Common Criteria offers major benefits, achieving Common Criteria certification is expensive and time-consuming process, making it difficult for smaller companies to participate
3. DoDIN APL (Department of Defense Information Network Approved Products List)
The United States DoDIN APL supported by the Defense Information Systems Agency (DISA) is a list of approved products that have passed cybersecurity (CS) and interoperability (IO) testing for use in DoD networks.
DoDIN APL follows the Unified Capabilities Requirements (UCR), ensuring all components work securely and efficiently. Testing includes cybersecurity checks using DoD Security Technical Implementation Guides (STIGs) and interoperability testing to confirm system compatibility.
Testing takes place in DoD-operated labs, where both cybersecurity and interoperability checks are performed. If a product passes, it receives provisional approval along with a Plan of Action and Mitigation (POA&M), which lists any issues found during testing. These issues usually need to be fixed within a year.
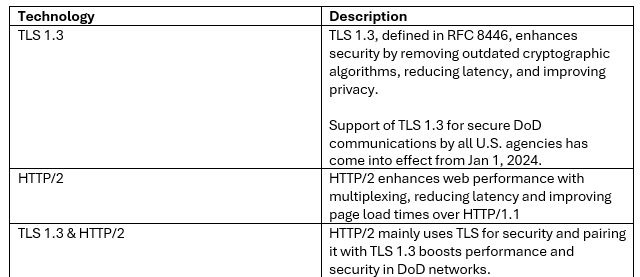
Two significant technologies relevant to DoDIN APL certification are TLS 1.3 and HTTP/2.
4. FedRAMP (Federal Risk and Authorization Management Program)
FedRAMP helps U.S. federal agencies like Department of Justice, Department of State, and Department of Commerce use secure cloud services by setting a common security standard for cloud providers. It modernizes IT while keeping federal data safe. Before FedRAMP, cloud vendors had to meet different security rules for each agency, making the process slow and repetitive.
FedRAMP simplifies this with a single security framework, allowing agencies to reuse approvals. Once approved, any agency can use the cloud service, saving time and money.
A FedRAMP-certified (Unified Communications as a Service) offering allows U.S. federal agencies to use secure cloud-based communication. Providers must meet strict security, performance, and technical standards to ensure reliability and compliance.
The FedRAMP Marketplace lists all cloud products that have received FedRAMP authorization.
5. GDPR (General Data Protection Regulation) Compliance
The General Data Protection Regulation (GDPR) protects personal data and privacy information in the European Union (EU), also setting rules for data sharing outside these regions. It gives people control over their data and creates standard rules for businesses. Unified Communications (UC) systems in Europe must follow GDPR, covering customer and employee data, call details, and storage rules.
Non-compliance can lead to heavy fines. Many UC vendors have strengthened security policies to meet GDPR and other laws like the California Consumer Privacy Act (USA) and Australia’s Privacy Act, ensuring their products comply with regulations and can be used in multiple countries.
6. HIPAA (Health Insurance Portability and Accountability Act) Compliance
HIPAA is a United States compliance law that sets rules for handling and safeguarding personal health information (PHI). It applies to doctors, hospitals, health insurers, and other organizations with access to patient data. Collaboration tools enable video consultations, medical report sharing, and online doctor-patient communication, requiring strict security.
Unified Communications (UC) solutions must follow HIPAA to be used in healthcare. Other countries have similar laws, like GDPR (EU), PIPEDA (Canada), Australia’s Privacy Act, and India’s DPDPA 2023. For UC solutions to work globally, they must comply with these laws, ensuring patient data stays secure no matter where it is accessed.
7. USGv6 (United States Government IPv6)
The United States Government IPv6 program (USGv6), established by NIST, aims to support U.S. government agencies in the widespread adoption of IPv6 products and services. It includes a standards profile (USGv6 Profile) and a product testing program (USGv6 Test Program) to ensure products comply with industry standards. These efforts align with existing IPv6 certification programs like [IPV6-Ready, IPv6-Forum] and [DODv6]. The latest version of this framework is USGv6 Revision 1 is USGv6 Revision 1 (USGv6-r1)
A list of USGv6-certified products, including Unified Communications (UC) solutions, can be found in the USGv6-r1 Product Registry | Interoperability Laboratory
IPv6 Ready Logo Program, developed by the IPv6 Forum, is a certification that verifies a product meets IPv6 standards and can work within an IPv6 network. For Unified Communications products and services, compliance with the IPv6 Ready Logo is essential for adoption by both public and private sector organizations worldwide.
Closing Thoughts
Technology is evolving rapidly, making secure communication essential for businesses, governments, and individuals. Unified Communications (UC) allows teams to connect from anywhere using AI, cloud, and automation. However, new technology also brings new risks. Cybercriminals use AI, deepfakes, and ransomware to steal data.
To stay safe, companies must follow strict security rules, use Zero Trust models, and encrypt communication. As UC advances, security must remain a top priority. Businesses should stay updated, use AI to detect threats, and promote a strong security culture.
The future of UC security is about staying prepared and ahead of cyber threats.








