Introduction
Risk appetite has quietly become one of the most misunderstood and underutilized tools in enterprise governance. For years, organizations treated it as a compliance artefact — a document created once, reviewed infrequently, and rarely connected to day‑to‑day decision‑making. That approach might have worked in a slower, more predictable world. It does not work anymore.
At its core, risk appetite defines the nature and extent of risk the enterprises are willing to accept while working toward their strategic objectives. It reflects Board and Management expectations about acceptable levels of uncertainty, loss, or disruption, and provides a reference point against which decisions, investments, and tradeoffs are evaluated across the enterprise.
Today’s operating environment is shaped by rapid geopolitical shifts, AI‑driven threats, quantum‑era uncertainty, and the deep convergence of OT, IT, cloud, and digital systems. Regulators across sectors are raising expectations, supply chains are more fragile than ever, and operational disruptions now carry consequences that extend far beyond financial loss.
In this landscape, risk appetite cannot be static. It must evolve into a living governance instrument — one that continuously reflects the organization’s strategy, technology footprint, and external environment.
This blog explores what a modern risk appetite framework looks like, why traditional models are no longer sufficient, and how organizations across industries can build a system that is measurable, resilient, and Board‑ready.
Why traditional risk appetite models are no longer enough
Many organizations still rely on qualitative statements such as “low tolerance for cyber risk.” These are well‑intentioned but ultimately unenforceable. Without quantified thresholds, they cannot guide decisions, justify investments, or withstand regulatory scrutiny.
Five forces are driving the need for a more dynamic approach:
1. Geopolitical Volatility
Sanctions, export controls, and supply chain weaponization now reshape risk exposure in real time. Appetite must explicitly address geopolitical scenarios.
2. AI as Both Attacker and Asset
AI‑powered phishing, deepfake social engineering, autonomous scanning, and model‑drift risks demand a formal AI risk appetite — something most organizations still lack.
3. Quantum Computing
With post‑quantum cryptography standards now published, “harvest‑now, decrypt‑later” risk is already live for organizations with long‑lived data or OT systems.
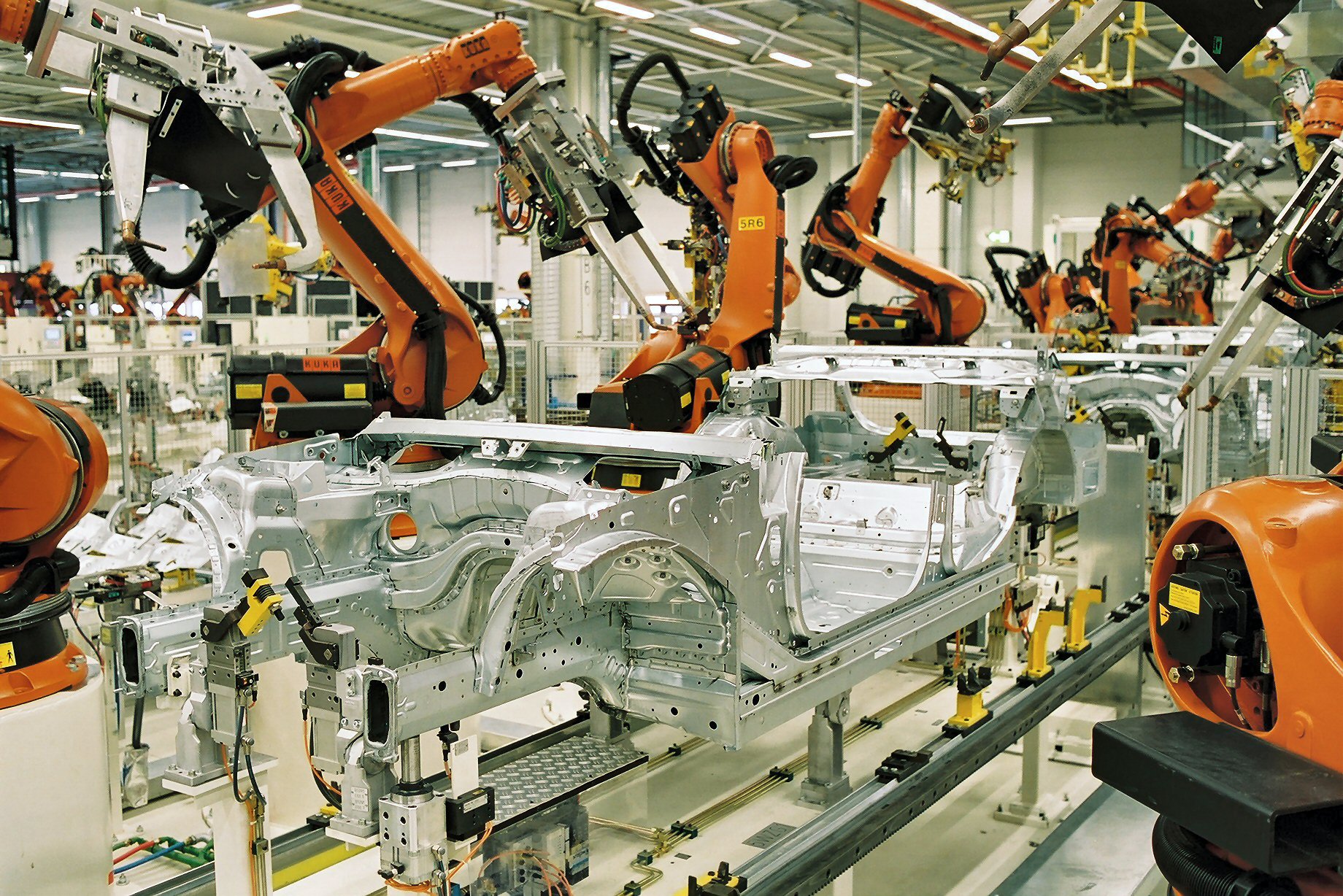
4. OT / IT / Digital Convergence
Operational systems — clinical systems, trading platforms, grid SCADA, plant controls — are increasingly network‑connected. Excluding them from risk appetite is no longer defensible.
5. Regulatory Acceleration
NIS2, DORA, the EU AI Act, HIPAA updates, SEC rules, and sector‑specific obligations now require demonstrable, quantified appetite.
A Modern Risk Appetite Framework: A Continuous, Connected System
A contemporary risk appetite model is not a document — it is an ecosystem. Seven components form the backbone:
1. Crown Jewels
Tier assets by consequence of compromise — not by who owns them. Critical operational systems must be included.
2. Business Impact Analysis (BIA)
Quantify disruption cost using RTO, RPO, MTPoD, and MBCO. These values directly set appetite thresholds.
3. Loss Expectancy & Cyber Risk Quantification
Convert risk into financial terms (ALE) and probability ranges (VaR). This is the bridge between the Board, the CFO, and the risk function.
4. CMDB
An authoritative inventory — including OT, medical devices, trading systems, and grid controls — is essential for meaningful quantification.
5. Setting Appetite
Board‑approved thresholds and KRI bands per risk category. No more qualitative‑only statements.
6. Controls & KRIs
ROSI‑based investment decisions and automated monitoring that signals when thresholds are approached.
7. Monitor & Adapt
A continuous loop. AI deployments, cloud migrations, M&A, geopolitical shifts, regulatory changes, and incidents must trigger immediate review.
What Good Governance Looks Like?
Across industries, mature organizations share five traits:
1. Board Ownership
The Board signs the appetite, reviews breaches, and understands the financial exposure.
2. Critical Systems in Scope
Operational systems — trading cores, EMR systems, grid SCADA, plant controls — are included in Crown Jewels, CMDB, and BIA.
3. Quantified Thresholds
ALE, VaR, and ROSI are standard inputs to decision‑making.
4. Supply Chain Reality
Concentration limits are explicit. Third‑party dependencies are mapped. Exceeding thresholds triggers escalation.
5. Living Governance
Appetite is refreshed every 6–12 months and whenever the environment changes.
The opposite patterns — qualitative‑only statements, OT excluded as “operations,” no quantification, no refresh triggers — are the root causes of major failures.
Four principles every organization must adopt
1. Critical operational systems must be in scope — no exceptions.
If a system can halt operations, harm patients, disrupt the grid, or stop trading, it belongs in the appetite framework.
2. Appetite must be expressed in financial terms.
“Low tolerance” is not governance. Boards must know the ALE and VaR for their top scenarios.
3. Refresh every 6–12 months.
The risk surface changes too quickly for multi‑year cycles.
4. Test resilience — do not declare it.
Failover, recovery, and manual fallback must be validated through exercises, not assumed.
When It Works — and When It Fails
1. When It Works — Hypothetical Scenarios
- Hypothetical Scenario A — Financial Services
A regional bank quantifies its risk appetite for the first time, calculating a $95M Value at Risk (VaR) for a large‑scale data breach. With quantified thresholds in place, the Board approves targeted controls, and automated KRIs are deployed within six months. Decision‑making becomes faster, more defensible, and aligned to financial exposure.
- Hypothetical Scenario B — Healthcare
A hospital network acquires a regional clinic group and uses the integration as a trigger to reassess its risk appetite. Crown Jewels and BIA exercises reveal gaps in clinical system resilience. New MTPoD thresholds are set, and inherited risks are quantified. The organization enters the post‑acquisition period with a clear, Board‑approved appetite position.
2. When It Fails — Hypothetical Scenarios
- Hypothetical Failure Scenario A — Energy Utility
An energy provider excludes grid SCADA systems from its risk appetite, treating them as “operations, not security.” A ransomware incident crosses into OT, forcing a 36‑hour suspension of grid operations. With no ALE, no MTPoD, and no regulator‑aligned thresholds, the organization faces €45M in losses and significant regulatory scrutiny.
- Hypothetical Failure Scenario B — Fintech
A fintech platform relies heavily on a single cloud provider but has no supply‑chain concentration thresholds in its appetite. When the provider experiences a major outage, the platform is offline for 18 hours. The incident exceeds what the Board would have considered acceptable — but no quantified appetite existed to guide decisions or investments.
Conclusion
Risk appetite is no longer a compliance checkbox. It is the mechanism that connects strategy, technology, and operational reality. Organizations that treat appetite as a living system — quantified, Board‑owned, OT‑inclusive, and continuously refreshed — make better decisions, recover faster, and avoid the blind spots that lead to crisis.
Those that don’t are increasingly exposed to risks they never intended to accept.
Bibliography
• IBM Security (2025) Cost of a Data Breach Report 2025
• Verizon (2025) Data Breach Investigations Report (DBIR) 2025
• World Economic Forum (2025/2026) Global Cybersecurity Outlook
• NIST (2024) Post‑Quantum Cryptography Standards
• EU (2022) NIS2 Directive
• EU (2022) Digital Operational Resilience Act (DORA)
• EU (2024) Artificial Intelligence Act
• ISO (2018) ISO 31000: Risk Management Guidelines
• COSO (2017) Enterprise Risk Management: Integrating with Strategy and Performance
Acronyms & Expansions
ALE — Annual Loss Expectancy
AI — Artificial Intelligence
ARO — Annual Rate of Occurrence
BIA — Business Impact Analysis
CMDB — Configuration Management Database
COSO ERM — Committee of Sponsoring Organizations Enterprise Risk Management
CRQ — Cyber Risk Quantification
DORA — Digital Operational Resilience Act
EMR — Electronic Medical Record
FAIR — Factor Analysis of Information Risk
HIPAA — Health Insurance Portability and Accountability Act
IEC 62443 — Industrial Automation and Control Systems Security Standard
ISO 31000 — International Standard for Risk Management
KRI — Key Risk Indicator
M&A — Mergers and Acquisitions
MBCO — Minimum Business Continuity Objective
MTPoD — Maximum Tolerable Period of Disruption
MTTR / MTTD / MTTRec — Mean Time to Repair / Detect / Recover
NIS2 — Network and Information Security Directive 2
OT — Operational Technology
PQC — Post‑Quantum Cryptography
RAS — Risk Appetite Statement
ROSI — Return on Security Investment
RPO — Recovery Point Objective
RTO — Recovery Time Objective
SCADA — Supervisory Control and Data Acquisition
VaR — Value at Risk