Overview
As a part of multi-cloud strategy ,organizations today are looking at interoperability for cloud-native enterprise applications or industry specific solutions like Infosys Revenue Management Platform SaaS cloud service. This solution is powered by Oracle Revenue Management and Billing (ORMB) and is a state-of-the-art cloud-native platform for core banking to support next-generation business modes.
One of the most common customer use cases is enablement of Single Sign-On (SSO) between Infosys Revenue Management Platform and customer specific Identity Providers. Infosys Revenue Management Platform SaaS supports federation via underlying cloud-native identity-as-a-service (IDaaS) platform, Identity and Access Management (IAM) with Microsoft Azure AD, Microsoft Active Directory ,OKTA and any other identity providers that support the Security Assertion Markup Language (SAML) 2.0 protocol. The scope of this blog is SSO configuration between Infosys Revenue Management Platform provided IAM (Service Provider) and Microsoft Azure AD (Identity Provider).
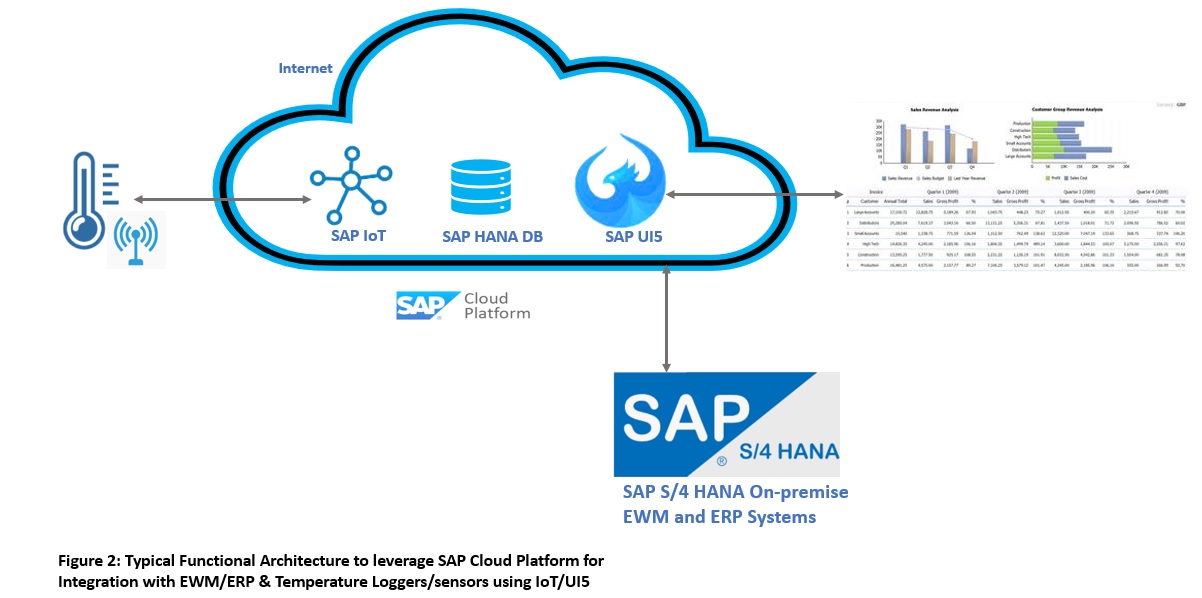
SAML 2.0 Integration Architecture – Infosys Revenue Management Platform SaaS and Azure Active Directory
SAML 2.0 is an XML-based markup language for security assertions incorporating three main roles – A user or principal ,identity provider (IDP) and service provider (SP).
Single Sign on functionality for Infosys Revenue Management Platform is supported by Security Assertion Markup Language (SAML) 2.0 protocol, which is an industry benchmark open standard for exchanging authentication & authorization data between an IDP (Azure AD in this case) and SP (Infosys Revenue Management Platform SaaS provided OCI Identity and Access Management).

SSO Configuration Workflow – Infosys Revenue Management Platform SaaS provided IAM and Azure AD
The overall configuration steps for enabling SSO between Infosys Revenue Management Platform SaaS provided IAM and Azure AD is shown below including the pre-requisites to configure the same.
- Download the Infosys Revenue Management Platform SaaS provided IAM Metadata XML file –To make the IAM Metadata XML file publicly accessible ,please navigate to domain “Default Settings” option and “turn on” the “Access Signing Certificate” option.Access the same via standard URL https://<IDCS-Service-Instance>.identity.oraclecloud.com/fed/v1/metadata in the browser without authentication. Right click on the XML document and save the same in local directory. To remove the public accessibility of metadata URL, turn off the option for signing certificate.

MS Azure tenancy with AD enabled
- Navigate to Azure AD on the Azure Portal Page and select the Azure Active Directory option.

- Create an Enterprise Application for Oracle IAM – In the default directory home page of Azure AD, select the “Enterprise Applications” option.

- Click on the “New Application” button.

- Azure AD has a gallery that contains thousands of enterprise applications that have been pre-integrated. Select “Oracle Cloud Infrastructure Console” as the option.

- Create the new Enterprise Application with OCI IAM as the name.

- Select the “Set Up SSO” option.

- Select the SAML protocol for SSO integration.

- Upload the OCI IAM Metadata XML file that we have downloaded in first step of this blog.For basic SAML configuration option the following are points of attention –
- “Identifier” MUST correspond to Oracle IAM SAML Provider ID ,the value of which is auto-configured.
- “Reply URL” MUST correspond to the IAM endpoint that is going to process the incoming SAML assertions sent by the Azure AD. This is also commonly known as the SAML Assertion Consumer Service. This value is also auto-configured as https://<IAM_host>/fed/v1/sp/sso, where <IAM-host> is the IAM host name exposed by Oracle Cloud.
- “Sign On URL” is populated as https://<IAM_host>/ui/v1/myconsole.

- Azure AD’s out of box configuration makes user.userprincipalname as the “User Identifier”. Leaving it like that will make Azure AD injecting a Name Identifier like “johndoe_myorg.com#EXT#@johndoemyorg.onmicrosoft.com” in the SAML assertion. Such identifier probably won’t exist in IAM identity store.

- Download the Azure “Federated Metadata XML” file and keep it handy for configuration in OCI IAM.

- Assign users to Oracle IAM application.
Only these users will be able to login into Azure AD and be federated to Oracle IAM. Click “Users and groups” link on the left pane and then “Add user” button on the right. Follow the wizard for having the users granted to the application.

Infosys Revenue Management Platform SaaS Cloud Service SAML Configuration
A quick way of creating users in Platform SaaS cloud service is via underlying default IAM console where on IAM Home Page, click “Users”, then the “Add” button for entering user data. Turn on “Use the email address as the user name” option as this is the scope of our SAML config.
- Identity Provider Basic Info – In IAM Default Domain Security tab, click the “Add SAML IDP” button.

- Enter Name and Description. Click Next.

- Import Azure AD metadata file into IAM – Check “Include Signing Certificate” to include it in signing certificate in IAM SAML requests for verification with Azure AD.

- Attribute Mapping – In the setup below, IAM ,at runtime, will try to match the incoming “Name ID” value in the SAML Subject to the “Username” attribute (user’s email attribute) on its user store. And since Azure AD is configured to send IAM user’s email address in the SAML assertion, the “Requested NameID Format” is “Email Address”. Click Next.

- IAM Metadata Download – No need to Download the Service Provider Metadata, since the SAML configuration is already done manually in Azure AD. Click Next for testing.
Note: Please note the values of “Provider ID” and “Assertion Consumer Service URL” MUST match “Identifier” and “Reply URL” values in Azure AD configuration.

- Test the Integration – Click “Test Login” button. A new tab should be opened and the browser redirected to Azure AD login screen for authentication. If there’s no user sync already done between Azure AD and IAM. If right credentials are provided, the browser should be redirected back to IAM test result page.


- Activate the Identity Provider – On the last screen of the Identity Provider creation, click “Activate” button and then “Finish”.

- “AzureAD” Identity Provider must now appear in the list of configured Identity Providers.

Add the IDP Policy for Azure to be implemented as your Identity Provider and for it to show on the Login Page.
- Create IDP policy rule – either add the IDP to the default (username-password) so it’s implemented on the Container level (all applications)

- Create new IDP rule on top of default policy and add runtime context (Application)

Result: When you access the application or use the IAM console, we have “Azure AD IDP” option as shown.Click the same and login via the common user defined in OCI IAM and Azure AD for SSO login.